- Início
- Top 10 Venice (Eyewitness Top 10 Travel Guides)
- Trading Chaos download
- The Military Balance 1991-1992 epub
- Advanced Accounting 9th Edition download
- The Cambridge History of Inner Asia: the
- A Practical Guide to Information Architecture
- Embedded Systems Interfacing for Engineers using
- The physics of liquid crystals download
- Project Valuation Using Real Options pdf download
- Abernathy
- statistical Digital Signal Processing and
- Practical Electronics for Inventors pdf download
- Chemical Reactor Analysis and Design Fundamentals
- Software Architecture Design Patterns in Java epub
- .NET Domain-Driven Design with C#: Problem -
- Botany in a Day: The Patterns Method of Plant
- Madeline pdf
- Test your English Vocabulary in Use
- Parallel Computer Architecture: A Hardware
- Pointing Out the Great Way: The Stages of
- Foundations of Economics: A Beginner
- Excel 2002 Para Dummies, Spanish Edition book
- Absolute Beginner
- Psychotherapy Relationships that Work: Therapist
- Riftwar Saga, Book 2: Magician: Master pdf free
- The Gift of Death book
- Playing For Real - A Text On Game Theory ebook
- The Practical Use of Fracture Mechanics ebook
- Microsoft Windows Server 2008 R2 Administration
- Reinforced concrete: design theory and examples
- W1FB
- Arduino Robotics ebook download
- Microsoft WSH and VBScript Programming for the
- Lectures on polytopes pdf free
- Practical DMX Queries for Microsoft SQL Server
- Solutions Manual for Modern Organic Synthesis
- Cuda Application Design and Development download
- Jewels of stringology pdf download
- Codex Alera 4 Captain
- Teach Yourself Gujarati pdf
- Capturing Sound: How Technology Has Changed Music
- An Introduction to Modern Econometrics Using
- A Critical Edition of Yeats
- Case Histories for the MRCP, 2nd edition book
- Continuous univariate distributions pdf download
- Journey to the End of the Night ebook
- Journey to the End of the Night ebook
- Schaum
- Measures, integrals and martingales pdf free
- Building Construction Illustrated, 2nd Edition
- The Visual Culture Reader book download
- Formulating Detergents and Personal Care
- The Complete Guide to Option Pricing Formulas
- Hydrodynamic and Hydromagnetic Stability ebook
- Surface science: An introduction ebook download
- Your Future In Forex!: The SECRET is yours...
- Refactoring Databases: Evolutionary Database
- Refactoring Databases: Evolutionary Database
- Enterprise Integration Patterns: Designing,
- Writing Up Research: Experimental Research Report
- New English File: Teacher
- Discrete-Time Speech Signal Processing:
- Don
- Basic and Clinical Endocrinology pdf download
- Canine and Feline Nutrition 3 edition: A Resource
- The Geological Interpretation of Well Logs 2nd
- Real Mathematical Analysis book download
- The 7 Habits of Highly Effective People: Powerful
- p-adic numbers: An introduction book
- BERKLEE JAZZ GUITAR CHORD DICTIONARY pdf free
- A Practical Guide to Stage Lighting, Second
- .NET Security and Cryptography book download
- Longman Language Activator ebook
- Teoria della predizione e del filtraggio pdf
- Il mulino di Amleto. Saggio sul mito e sulla
- A Radical Approach to Lebesgue
- Technical Analysis & Options Strategies book
- Module theory: an approach to linear algebra book
- Asian Noodles: Science, Technology, and
- Advanced Machining Processes book download
- Solar Queen 04, Postmarked the Stars (1969) ebook
- Programming in the OSEK/VDX Environment pdf
- Plasma Antennas ebook download
- BS ISO/IEC 27035:2011 Information technology.
- Fundamentals of Cavitation book
- Front Office Operations & Management book download
- Extreme Programming Refactored: The Case Against
- Differential Equations: A Modeling Perspective
- Legal English: How to Understand and Master the
- Java Deployment with JNLP and WebStart pdf
- Schaum
- Handbook of Logistics and Distribution
- BRS Physiology, 5th Edition (Board Review Series)
- Continuous univariate distributions download
- Differential Geometry, Lie Groups and Symmetric
- A Guide to Equine Joint Injection and Regional
- Oracle JDeveloper 11g Handbook download
- Programming in Haskell epub
- Knitting Mochimochi: 20 Super-Cute Strange
- Molecular Evolution: A Phylogenetic Approach book
- The Body in Pain: The Making and Unmaking of the
- Psychic Vampire Codex: A Manual of Magick and
- Analog Days: The Invention and Impact of the Moog
- C Gui Programming With Qt4 pdf download
- Power Line Communications in Practice book
- Free audiobook download uk The Marvel Book:
- Descargar libro de la selva LE PETIT PRINCE: AVEC
- Best sellers eBook Professor at Large: The
- Ebook nederlands descargar gratis HOMBRES DE MAIZ
- Libros gratis para descargar en línea. DELTA DE
- Descarga un libro de google books mac YOUR NAME
- Descarga gratuita de libros de texto en pdf LA
- Ebook free downloads pdf Edison
- Ebook free downloads pdf Edison
- Read online books free no downloads Eneagrama, el
- Book downloading portal Sparkson's Illustrated
- Téléchargements manuels gratuits pdf Comme une
- Ebook torrents téléchargement gratuit
- Forum pour le téléchargement d'ebook Cahier de
- Livres gratuits à télécharger sur tablette
- Free download pdf ebooks We Must Be Brave
- Free full download of bookworm Learn to Draw
- Ebook pdf file download End of Days MOBI RTF iBook
- Free ebooks for mobiles download Plunderer, Vol.
- Télécharger Google book en pdf mac La
- Livres électroniques gratuits téléchargeables
- Download ebooks for ipods How to Date Men When
- Free ebook downloads from google books Komi Can't
- Libros para descargar en ipods PERVERSO SEDUCTOR
- ¿Es posible descargar libros gratis? EL CANTAR
- Epub ebook download torrent More Than Enough:
- Free ebooks pdf format download Batman: Detective
- Epub download book The Soulful Art of Persuasion:
- Downloads free ebook The Girl without Skin
- Download books on ipad mini Apache Oozie
- Scribd download book Outlaws 9781492651314 MOBI
- French books pdf download Apocalypse Now Now
- Ebooks for download cz I Ching: The Essential
- Ipod audio books download Comrade J: The Untold
- Download free books for iphone kindle Muhyo &
- Free torrent downloads for books Something Worth
- Download ebooks in word format Building Outrigger
- Télécharger le format pdf gratuit ebook Eloge
- Téléchargements ebook Pdb Punchlines - Petit
- Forum pour le téléchargement d'ebook Français
- Téléchargements de livres audio gratuits itunes
- Download books for free for kindle Statistics
- Full book download free Type for Type: Custom
- Ipod downloads audio books Jazz Fly 3: The
- Read free books online free no downloading The
- Ebook for download free in pdf Even the Saints
- Epub books free download for android
- Ebook rar download 3 Stepbrothers PDB DJVU
- Download new books for free Small Teaching
- Free audiobook download links Where Winter Finds
- Textbook downloads free The Planets in English by
- Ebook pour l'électronique de base
- Téléchargements ebook gratuits en ligne
- Libros gratis en línea para descargar ANTOLOGIA
- Descargar libro real pdf EL ASESINO DE
- Libro electrónico gratuito para descargar
- Descargar libro gratis italiano SOS...
- Google books download To the Eastern Seas: Thomas
- Download e book free online From the Ashes: My
- Libro de audio gratis descargar libro de audio
- Descarga gratuita de libros en pdf para kindle.
- Free books download ipod touch The Loud House #7:
- Free books download in pdf file Moxie
- French textbook download Crudo 9780393652727 by
- Free download ebooks for android The Lost
- English book for download Love and Other Words in
- Free computer books downloading Dreams Come to
- Ebook kindle portugues download Can't Hurt Me:
- Download ebooks free literature The Thousand
- Download books magazines ipad Persepolis Rising
- eBooks for free Heal: Discover Your Unlimited
- Free ebooks to download for android tablet Life
- Textbook direct download This Is Me: Loving the
- Online pdf ebook free download Storytelling with
- Epub download ebook The Golden Tower (Magisterium
- Publication de l'eBookStore: Un jour en décembre
- Téléchargez google books en pdf gratuitement en
- Free e book downloads Tiamat's Wrath by James S.
- Free ebook download uk Taste of Home Copycat
- Descargas gratuitas kindle libros en línea
- Descargas de libros de texto de audio EL LEGADO
- Download ebooks in pdf for free The Crow's Call:
- Download free google play books The A List
- Ebook for psp free download 2020 North American
- Ebook free download german IT'S ALL IN YOUR HEAD
- Nuevos ebooks de descarga gratuita. EL ULTIMO
- Los mejores ebooks 2013 descargados ORAGE SUR LE
- Descargar ebook gratis gratis TODO LO QUE NUNCA
- Descargar música de audio libro PISO PARA DOS
- Descargas de audiolibros completas gratis VAS A
- Descargar libro electronico SIEMPRE SOÑÉ
- Free ebook downloads ipods Crier's War
- Free database books download Diary of a Dummy
- Ebooks em portugues free download The Lady's
- Free new books download Angel in a Devil's Arms:
- Téléchargement gratuit ebook j2ee Oxygène
- Livres à télécharger gratuitement au format
- Libros en pdf descarga gratuita TU AÑO PERFECTO
- Descargar el libro de texto pdf SERE FRAGIL in
- Enlaces de descarga de libros de epub EL PECADO
- Audiolibros en inglés con descarga gratuita de
- Los mejores libros electrónicos gratis descargar
- Libros de Epub para descargar gratis LA CARNE de
- Descargar libro fácil para joomla SOY
- Descargar Ebook gratis kindle EL NEGOCIO DEL AGUA
- Download books on kindle for free Quantum
- Free pdf it ebooks download The Plant Paradox
- Google download books The Andromeda Evolution
- Free audio books to download uk Robert Kirkman's
- Télécharger des livres gratuits en ligne
- Amazon télécharger des livres sur bande L.A.
- Free it pdf books free downloads When You Know
- Free downloadable ebooks for kindle fire
- Téléchargement gratuit d'ebook au format txt
- Télécharger le format ebook txt Octobre noir
- Descargar ebooks in txt gratis COSTURA PARA
- Libro de ingles gratis para descargar UN LUGAR
- Book download Remains in English
- Download textbooks torrents The Midwinter Witch
- Ebooks download kostenlos pdf Danny Flash and the
- Epub free ebooks downloads MAIN GAUCHE Grim &
- Open source ebooks free download La Resolucion
- Download electronic books ipad My Year of Rest
- Download google ebooks nook The Secret Language
- Mobi ebook download forum Rhodesian Light
- Download free books online for ibooks The Gang of
- Download ebooks for kindle Even the Saints
- Descargar libros de francés ibooks CONFESSIONS
- Descargar en linea NIGHT WITHOUT END (OBL 6:
- Téléchargements gratuits de livres audio pour
- Livres audio anglais téléchargement gratuit
- Téléchargement du livre électronique en ligne
- Real book téléchargement gratuit pdf Un secret
- Free download book Becoming America: Highlights
- Ebook ita download gratuito Let's Learn Kanji: An
- Téléchargement de livres pdf en ligne LOL Tome 2
- Forums pour télécharger des ebooks Psychologie
- Descargar libro gratis para android ORAL
- Descargar ebooks gratuitos para iphone LA
- Free audo book downloads Boruto, Vol. 7: Naruto
- Ebook free download txt She's With Me FB2 PDB
- Download books to iphone free Sweat the
- Download ebook pdf The Change Masters
- Download books for free pdf The Play (Briar U,
- Online google books downloader A Winter's Promise
- Download ebook pdf online free Imagine Out Loud:
- Free book download for kindle 'Nam: The Vietnam
- Online ebook downloads The Passengers
- Free book downloads mp3 Backlash 9781982104047
- Contatos
Total de visitas: 79113
.NET Security and Cryptography by G. Gnana Arun Ganesh, Peter Thorsteinson
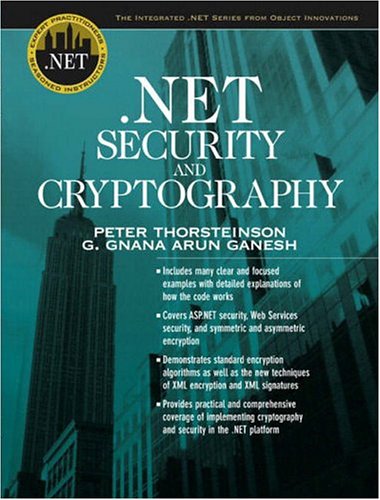
Download eBook
.NET Security and Cryptography G. Gnana Arun Ganesh, Peter Thorsteinson ebook
ISBN: 013100851X, 9780131008519
Page: 496
Format: chm
Publisher: Prentice Hall
Use the Windows Security and Cryptography APIs. We recommend that all customers immediately apply a workaround (described below) to prevent attackers from using this vulnerability against your ASP.NET applications. Security.Cryptography.X509Certificates.X509Certificate certificate, System.Security.Cryptography.X509Certificates.X509Chain chain, System.Net.Security.SslPolicyErrors sslPolicyErrors) { return true; };. Build and deploy robust Visual C++ . A Simple Encrypting and Decrypting class can be built in .net using System.Security.Cryptography Namespace. Papers are divided in topical sections on public key encryption, digital signature, block ciphers and hash functions, side-channel attacks, zero knowledge and multi-party protocols, key management, authentication and identification, privacy and anonymity, RFID security and privacy, and internet security. Applied Cryptography and Network Security By Jianying Zhou, Moti Yung English | 2010 | 577 Pages | ISBN: 3642137075 | PDF | 6,6 MB This book constitutes the. Publisher: Prentice Hall PTR; 1st edition (August 29, 2003) Language: English ISBN-10: 013100851X ISBN-13: 978-0131008519. [Level T2] .NET Framework provides a set of cryptography services in System.Security.Cryptography namespace. This vulnerability exists in all versions of ASP.NET. NET Framework, handling database integration, ensuring security, creating administrative tools, and much more. Review of .NET Framework cryptography and symmetric algorithms benchmark. RNGCryptoServiceProvider generates an upredictable, and therefore cryptographically valid, sequence of psuedorandom numbers and stores them array of type byte. This vulnerability was publically disclosed late Friday at a security conference. To understand how this vulnerability works, you need to know about cryptographic oracles.
Field theories of condensed matter systems pdf free
A History of Knowledge: Past, Present, and Future book download

